Data breach statistics have continued to climb at an alarming rate in 2016, with a staggering number of incidents exposing several billion personal records thus far this year.
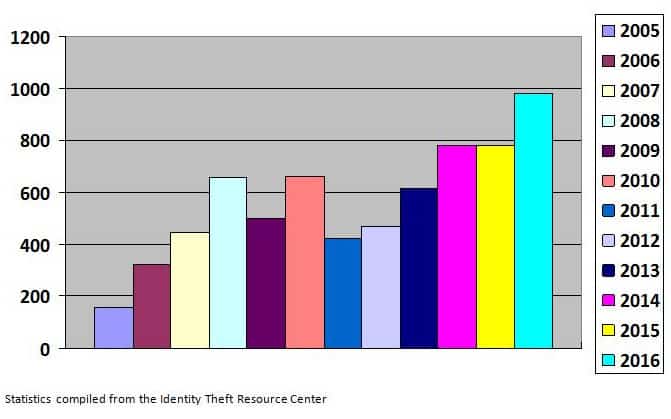
In fact, according to the Identity Theft Resource Center (ITRC), a non-profit organization established to support victims of identity theft and broaden public education and awareness in the understanding these crimes, there have been 980 reported breaches as of December 13th of this year, already a record number of incidents since ITRC began keeping these records in 2005.
As most in the retail loss prevention industry a well aware, a data breach is a security incident in which sensitive, protected or confidential information is copied, transmitted, viewed, stolen or used by an individual unauthorized to do so. Data breaches come in many forms, and may involve financial information such as credit card or bank details, personally identifiable information such as social security numbers and other sensitive information, company trade secrets or intellectual property, personal health information, and other forms of sensitive and protected information. Most data breaches involve overexposed and vulnerable unstructured data – files, documents, and sensitive information.
The various types of data breaches that have occurred over the past year have touched businesses of all kinds, with current data breach statistics indicating that once again this year there have been many high-profile incidents, including recent incidents which include 2 separate attacks on Yahoo (impacting more than 1 billion and 500 million user accounts respectively), LinkedIn (more than 117 million accounts), government agencies including the U.S. Department of Justice and the Internal Revenue Service, and retailers such as Wendy’s and Verizon. Showing that cyber-criminals don’t discriminate, a recent data breach reported has revealed that AdultFriendFinder, an X-rated website, was the victim of an immense breach, with approximately 412 million users having personal information stolen and published in online criminal marketplaces.
While cyber-criminals may not discriminate as far as where they steal information, the retail industry and other businesses still tend to be a prime target. Thus far this year data breach statistics once again show that business-related data breaches have led the pack, with 432 incidents thus far in 2016.
Retailers are now deeply committed to improving their data security efforts, and many have invested millions of dollars to improving data protection strategies throughout their organizations. However, it is still the responsibility of every retail employee to do their part to combat all kinds of cyber crimes. Here are a few tips to help manage your data security programs:
- Limit the number of third parties you give your information to.
- Annually assess all potential IT risks and exposures and perform frequent testing of all controls related to the monitoring and protection of data.
- Establish a written policy about privacy and data security and communicate it to all employees. Educate them about what information is sensitive and their responsibilities to protect that data.
- Control the use of computers. Restrict employee use of computers to business. Block access to inappropriate websites and prohibit use of unapproved software.
- Secure all computers, implementing password protection and requiring re-logon after a period of inactivity. Train employees to never leave laptops or PDAs unattended.
- Keep security software up-to-date. Use firewalls, anti-virus and spyware software; update virus and spyware definitions regularly.
- Manage use of portable media. DVDs, CDs and USB flash drives are more susceptible to loss or theft.
To learn more about controlling data breaches, read Building a New Data Security Defense Team from LP Magazine.